Sophisticated Attacks
Bad Actors are Employing Increasingly sophisticated attacks
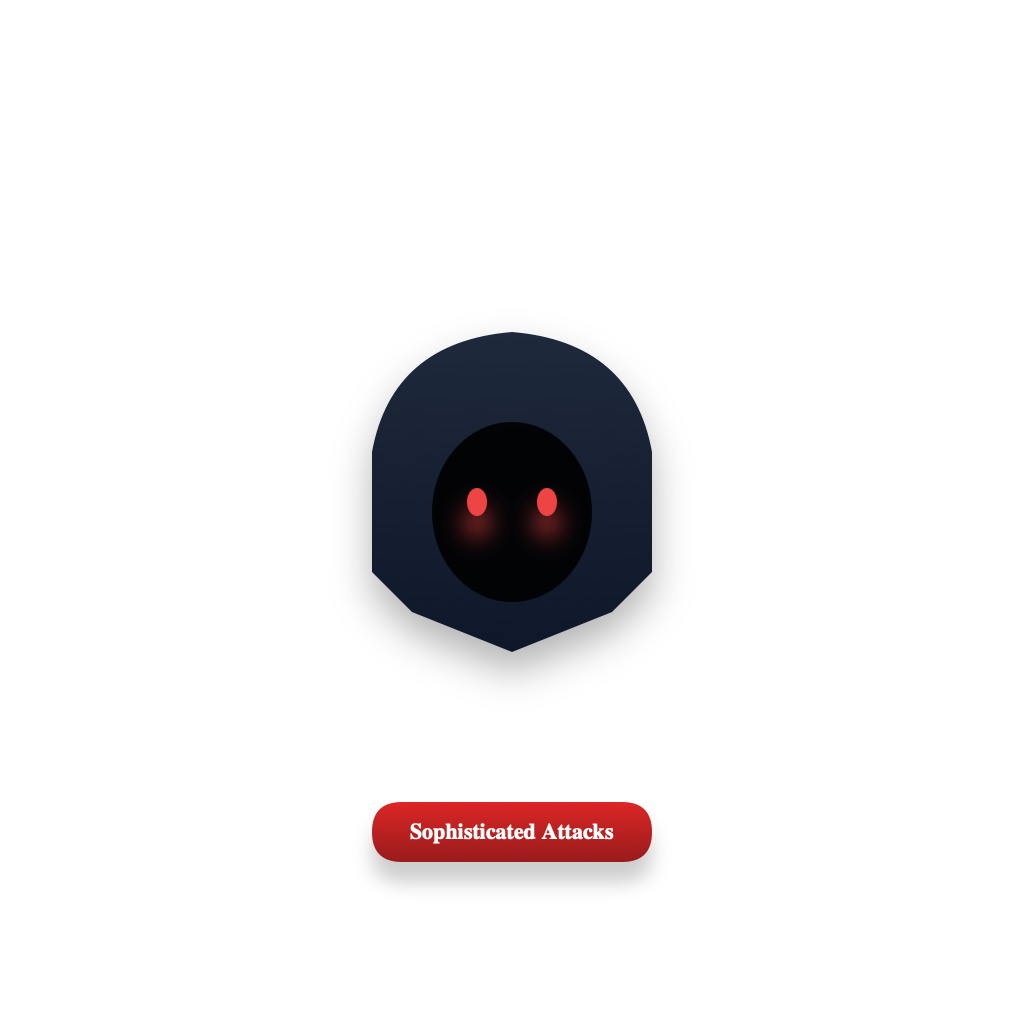
Evolving Digital Estate
Securing the ever-growing and evolving digital estate is challenging.
Overwhelming Signals
Intelligent correlation and action on an overwhelming amount of threat signals is challenging, time-consuming, and costly.