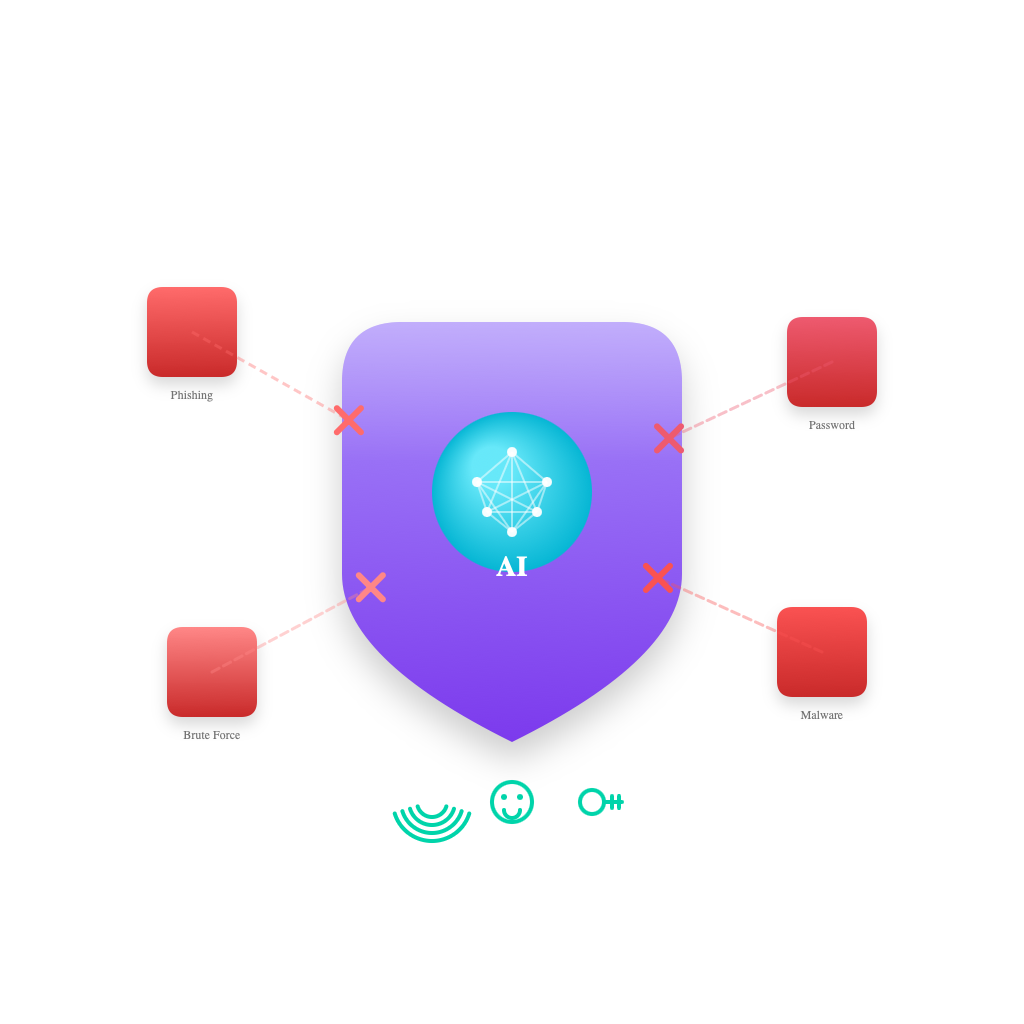
Prevent Identity Attacks
Take advantage of game-changing generative AI risked-based access policies, and phishing resistant, password free authentication to block attacks and protect your workforce, customers and machine identities.
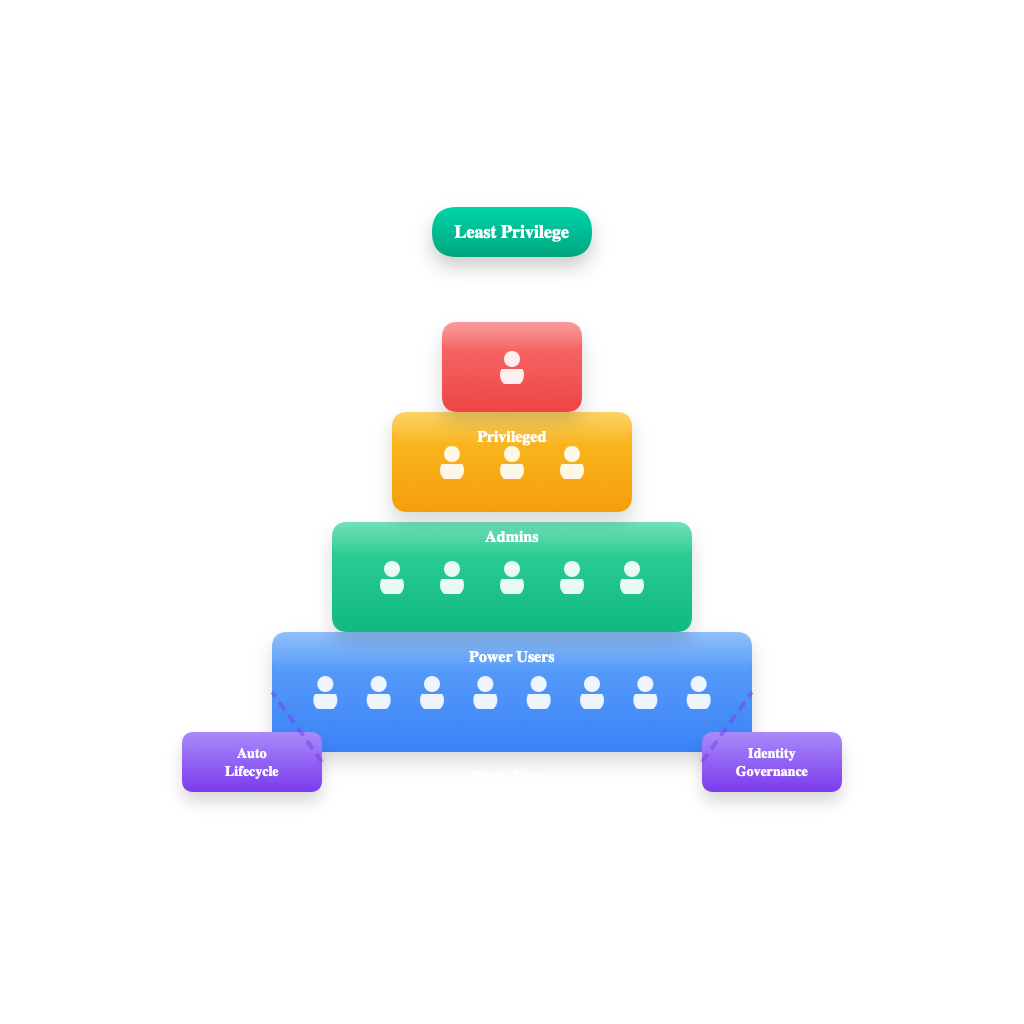
Enforce least-privilege access
Automate identity governance, lifecycle workflows, and privileged-access management to give every identity the right level of access to any app or resource, with full visibility and data-driven remediation.
Unify access controls
Reduce complexity and accelerate your Zero Trust path by extending adaptable conditional access policies and access controls across identities, endpoints, and public and private networks.
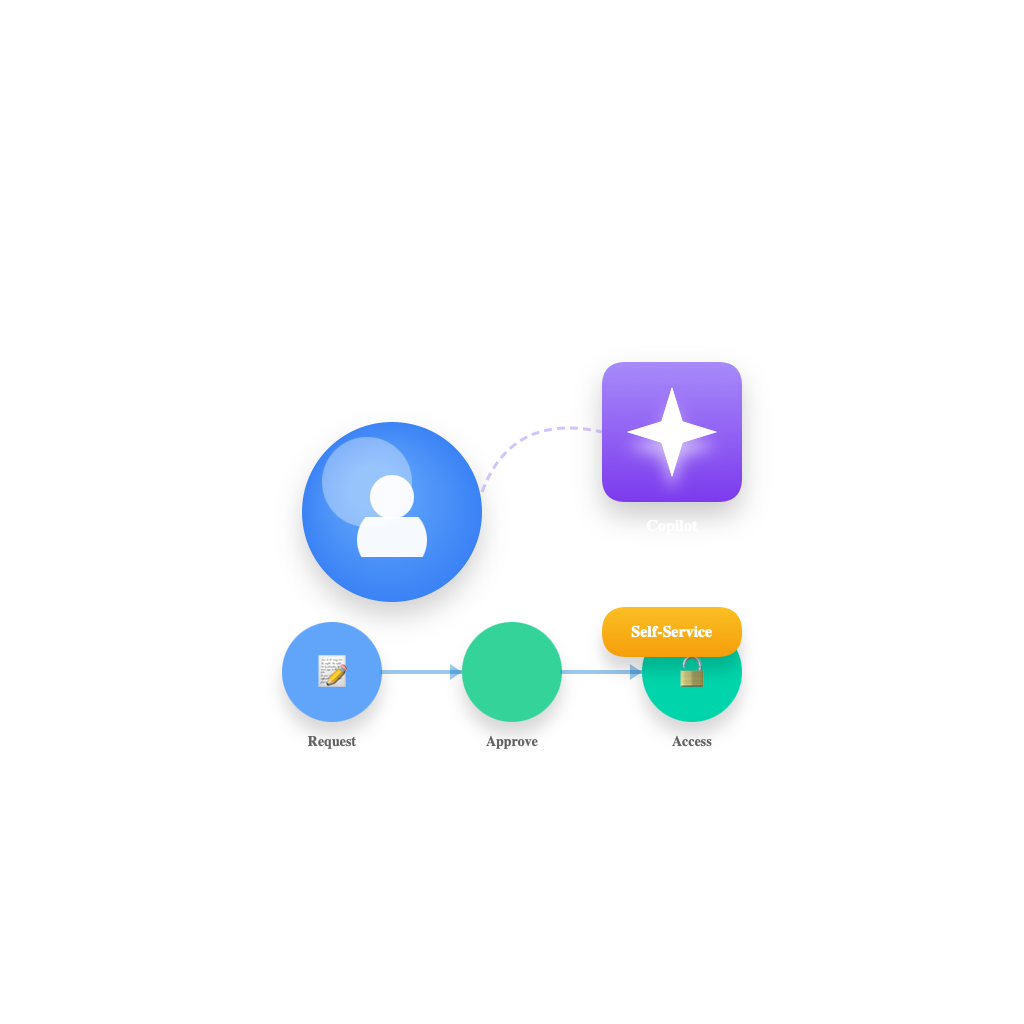
Improve the user experience
Streamline identity and network access workflows and get tailored guidance from natively embedded Security Copilot. Give workers and customers faster, self-service access to what they need.