Eligible Workloads

Microsoft Defender XDR
Microsoft Sentinel
Our strategic, risk-focused approach spans collaboration, identity, endpoint, and data environments, empowering you to take control of your cybersecurity landscape.
FIND OUT WHAT I QUALIFY FOROur strategic, risk-driven approach leverages Microsoft Defender XDR across identity, endpoint, email, collaboration, and data environments to give you unified visibility and control over your security posture. Through focused threat detection, exposure analysis, and hands-on validation, we deliver immediate, prioritized recommendations that reduce risk fast. Each engagement culminates in a Zero Trust–aligned roadmap that strengthens detection, response, and prevention capabilities—improving control effectiveness today while hardening your organization against tomorrow’s threats.

Designed to be thorough yet efficient — minimum disruption, maximum evidence.
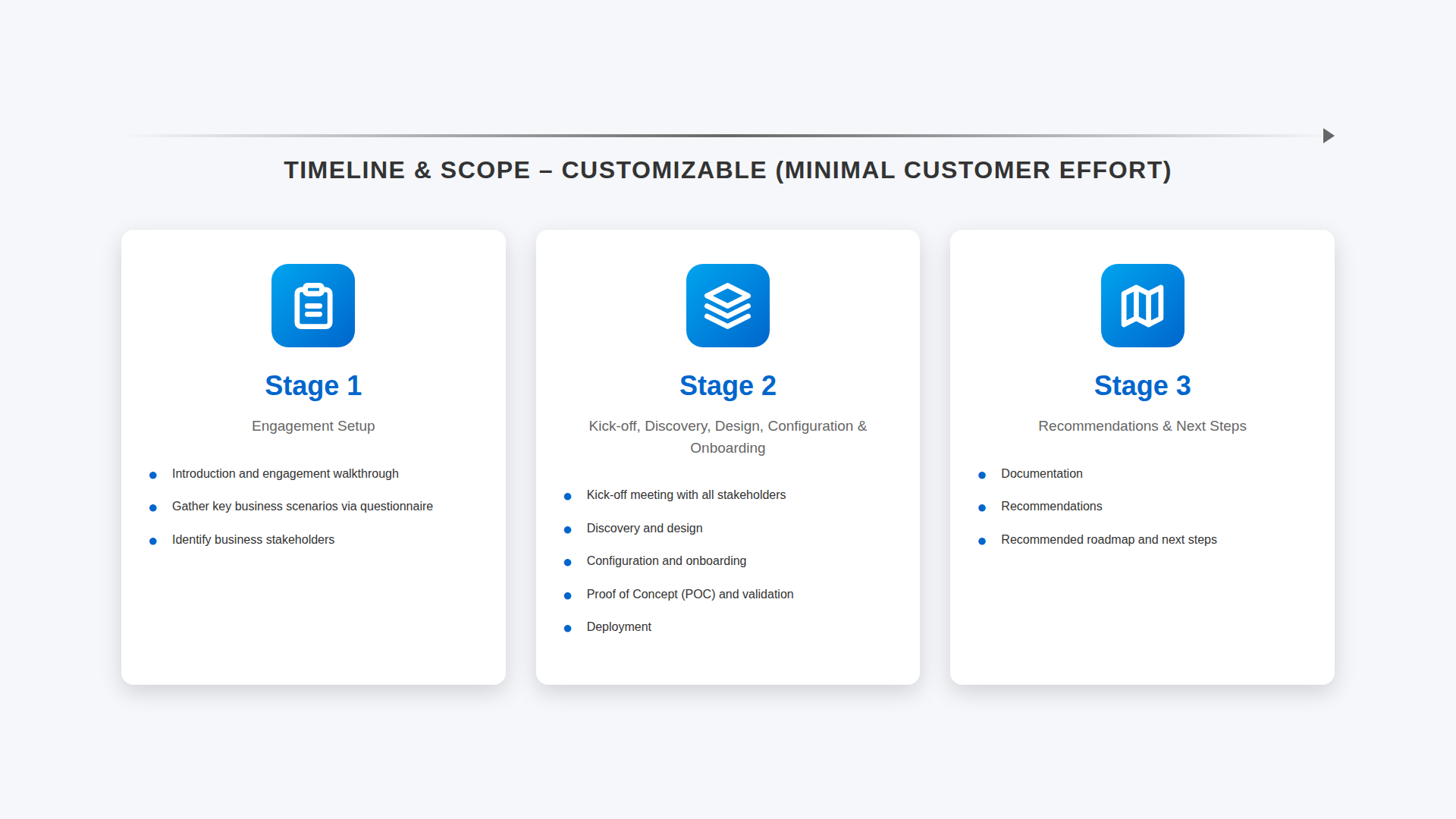
Weeks delivered in structured phases with defined milestones and a final readout session.
Hours of scheduled sessions covering kickoff, Configuration, review phases, Deployment, risk walkthrough, and executive readout.